Release 11.0
Explore the release highlights for Software AG Cloud version 11.0.
Explore the release highlights for Software AG Cloud version 11.0.
To improve security and enhance the user experience, a browser session expiration alert has been introduced. Previously, users were not notified about session expiration, which caused the page to become unresponsive. Any action by the user revalidated the session and automatically logged them in, interrupting tasks after being idle. Now, a notification will appear on the screen a few minutes before the session is set to expire, providing an option to either continue the session or log out. If the user does not act on the notification within the given timeframe, they will be automatically logged out and prompted to log in again.
A captcha mechanism has been introduced to mitigate the issue of email flooding in the Forgot Environment Name scenario. Now, when there are multiple requests, the captcha will be activated to guard against attacks.
Software AG Cloud documentation now includes a dedicated section for FAQs, addressing frequently asked questions and providing answers to common queries.
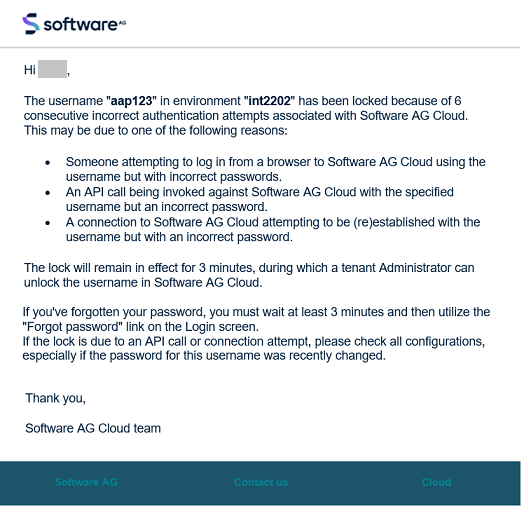
Prior to this release, a single user locked email was sent after the initial sequence of 10 invalid authentication attempts within a short time window. Now, upon expiration of the temporary lock (by default after 5 minutes), if additional invalid authentication attempts occur, more emails are sent. These emails include information on the number of attempts made and the duration of the ongoing temporary lock. This enhancement facilitates troubleshooting scenarios where temporary locks are triggered by a connection or API call with invalid credentials that repeatedly attempt authentication.
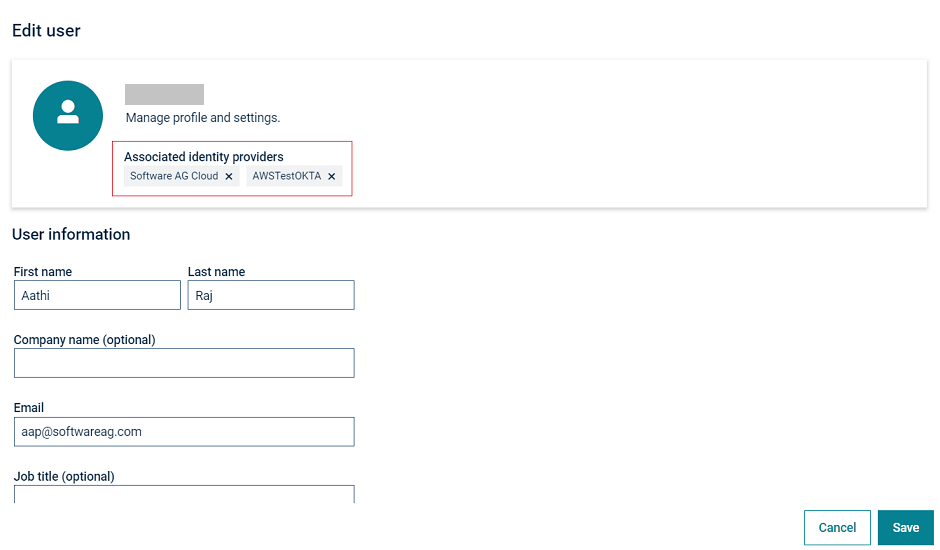
When the Allow login if username exists setting of Single sign-on is enabled, Software AG Cloud users can log in from multiple Identity Providers (IdPs) linked to a single user profile. This can make it convenient for the same user to log in via different Identity Providers, but it does add some uncertainty regarding the security roles of such users.
With this release, a Cloud Tenant Administrator or an Account Administrator can now disconnect (forget) the user from any of the Identity Providers, ensuring that at least one remains linked. This allows administrators to correct undesired instances of users with multiple Identity Providers, providing them with more control over the associated security roles.
The user locked email has now been enhanced to offer additional information about the potential causes for the account lock. It provides guidance on the required actions, including details on the number of consecutive incorrect authentication attempts associated with Software AG Cloud and the duration of the user lock until when it will remain in effect.
Prior to this release, the webMethods.io API Gateway and webMethods.io Developer Portal were bundled together when requesting a Free Forever edition of webMethods.io API. Now, each product can be subscribed independently, and each has its own lifecycle.
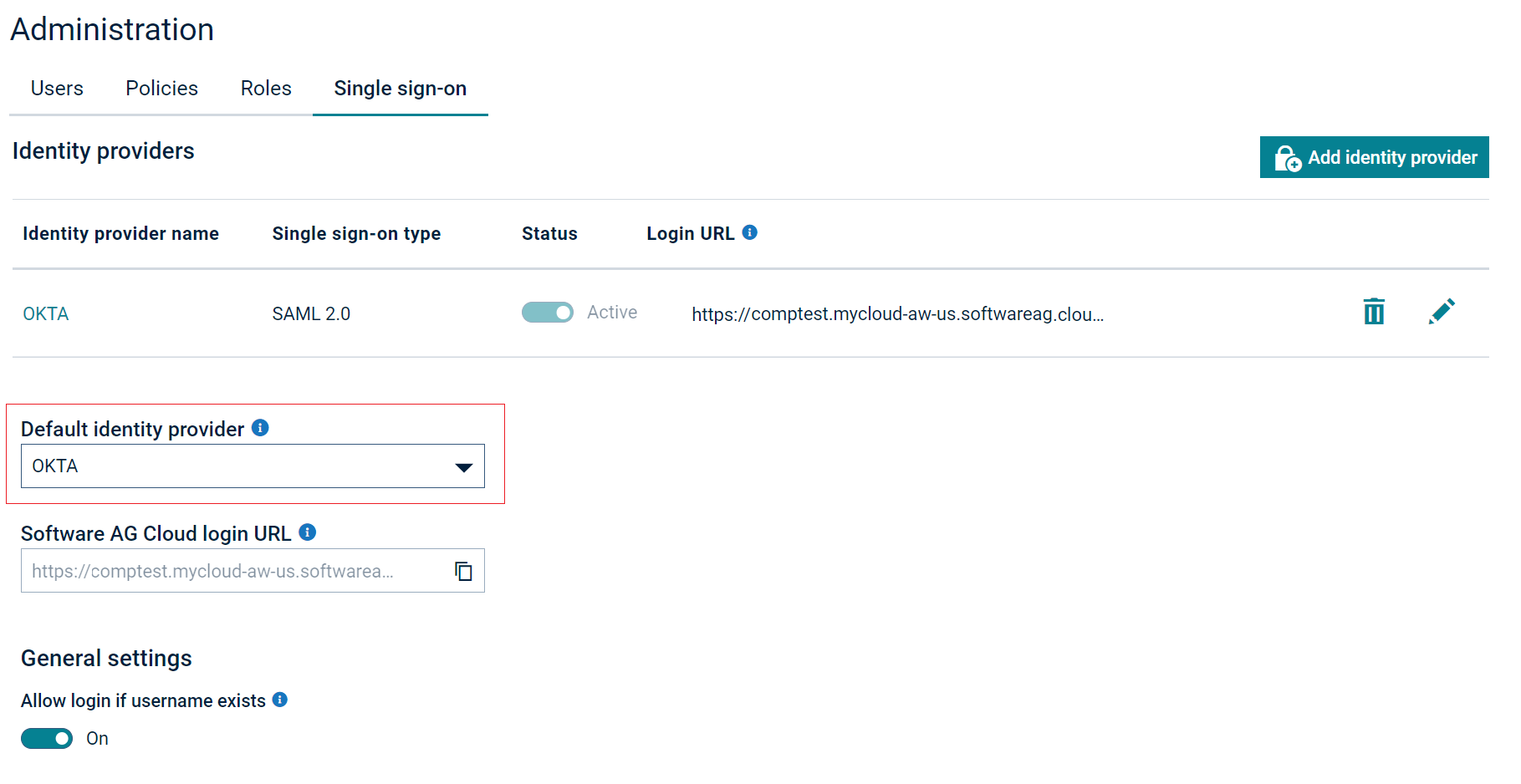
You can now configure any external identity providers as the primary identity provider (IdP) to authenticate users for Software AG Cloud products.
With this newly added feature, you can set an external IdP as the Default identity provider on the Single Sign-On (SSO) page and use a direct login URL for your identity providers.
As part of our efforts to upgrade and optimize our Azure infrastructure, we intend to substitute the current NAT IP addresses with new IP addresses. This modification will have implications for products such as webMethods.io Integration, webMethods.io B2B, webMethods Cloud Container, webMethods.io API Gateway, and webMethods.io Developer Portal.
The activation of these new NAT IP addresses is scheduled as per the information provided in the webMethods.io iPaaS Status page. Note that the old IP addresses, previously permitted on the firewall, will cease functioning, potentially affecting the usability of our products. To ensure uninterrupted access to our products, ensure that the specified new NAT IP addresses are added to the firewall’s allowed lists.
| Old IP Addresses (To be removed) |
New IP Addresses webMethods.io Integration, webMethods.io B2B, and webMethods Cloud Container |
New IP Addresses webMethods.io API Gateway, and webMethods.io Developer Portal |
|---|---|---|
|
|
|
| Old IP Addresses (To be removed) |
New IP Addresses webMethods.io Integration, webMethods.io B2B, and webMethods Cloud Container |
New IP Addresses webMethods.io API Gateway, and webMethods.io Developer Portal |
|---|---|---|
|
|
|
| Old IP Addresses (To be removed) |
New IP Addresses webMethods.io Integration, webMethods.io B2B, and webMethods Cloud Container |
New IP Addresses webMethods.io API Gateway, and webMethods.io Developer Portal |
|---|---|---|
|
|
|